Google Reviews Management: How to Handle Negative Feedback and Increase Positive Reviews
When checking Google Maps, store details along with customer ratings and reviews can be seen. Many people rely on these…

When checking Google Maps, store details along with customer ratings and reviews can be seen. Many people rely on these…
Did you know that many job search websites allow current and former employees to post reviews about their experience working…

Are Negative Search Results Hurting Your Business? Here’s How Reverse SEO Can Help If you’ve ever searched for your company…
1.2 Why is it being highlighted? One reason reputation risk has gained attention is the development of the internet, which…
Defamation on social media is extremely common and continues to be a persistent social issue. There have even been cases…

Mistake 1: Weak Passwords Weak passwords are one of the most common security vulnerabilities and yet, they’re also one of…

What Are Dupes? Dupes are products that mimic the look and feel of higher-end items but are sold at a…

Social Media Impersonation Social media presence is incredibly important for modern brands. This is both because it allows brands to…
Risks Associated with Inadequate OPSEC Measures Without proper OPSEC measures, businesses are at risk of data breaches, intellectual property theft,…
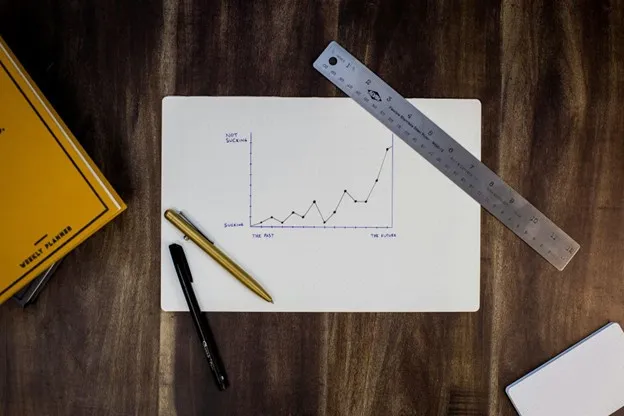
At its core, brand lift is about understanding the incremental impact of your marketing efforts. By comparing consumer perceptions before…